
ITAR & AI-Enabled Defense Technologies: Autonomous Systems, Targeting Algorithms, and the New Export-Control Frontier
Artificial intelligence has moved from research laboratories into deployed defense systems: autonomous ISR platforms, battlefield decision-support engines, predictive logistics tools, electronic-warfare optimization software, and AI-enabled targeting modules.
For U.S. companies operating in this field, particularly startups collaborating with the Department of Defense, the key question is no longer whether hardware is export-controlled. The more complex inquiry is whether algorithms, training data, model weights, simulation environments, and engineering collaboration workflows constitute “technical data” or “defense services” under the International Traffic in Arms Regulations (“ITAR”).
In 2026, AI-driven defense innovation is colliding with a regulatory structure originally designed for missiles, schematics, and physical components. The resulting legal exposure may include civil penalties, criminal liability, debarment, reputational harm, and parallel sanctions risk.
This article examines how AI-enabled defense technologies trigger ITAR jurisdiction, where enforcement exposure is emerging, and how companies should structure compliance frameworks in this evolving environment.
I. The ITAR Framework Applied to Artificial Intelligence
ITAR, administered by the Directorate of Defense Trade Controls (DDTC) within the U.S. Department of State, regulates:
- Defense articles listed on the U.S. Munitions List (USML)
- Technical data directly related to defense articles
- Defense services
Historically, export-control analysis centered on tangible hardware: aircraft, missiles, armored vehicles, and avionics. AI disrupts this paradigm by introducing three recurring classification questions:
- Is the AI model itself a defense article?
- Does source code, model architecture, or training data constitute “technical data”?
- Does collaboration in training or integration constitute a “defense service”?
The analysis no longer focuses solely on physical exports. It turns on whether AI functionality enhances combat capability or supports USML-controlled systems.
II. When AI Becomes “Technical Data”
ITAR defines “technical data” broadly to include information required for the design, development, production, manufacture, assembly, operation, repair, testing, maintenance, or modification of defense articles.
In the AI context, this may include:
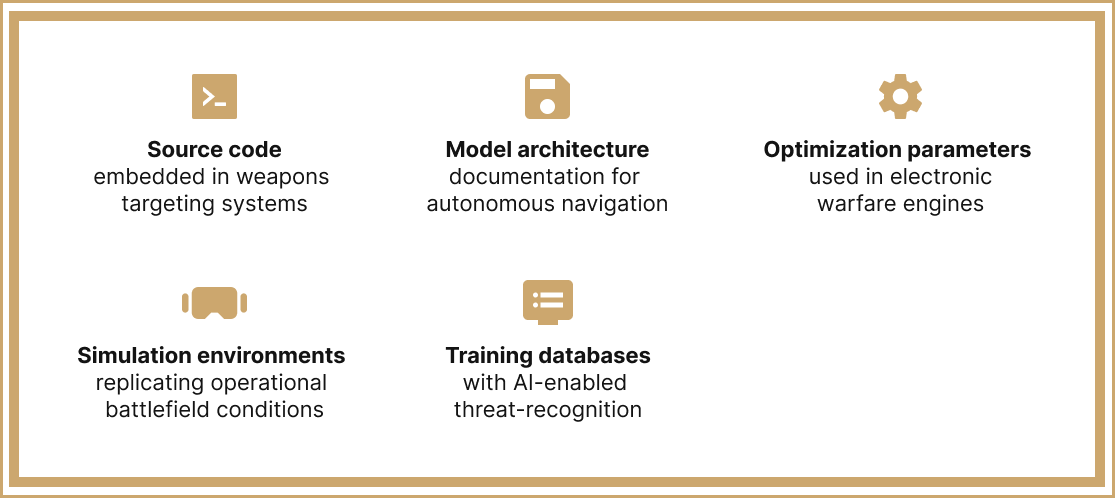
Practical Regulatory Reality
If an AI system is:
- Specially designed, developed, configured, adapted, or modified for a USML-listed defense article; or
- Integrated into controlled weapons platforms;
then associated model artifacts may themselves constitute controlled technical data.
A persistent misconception is that “software is not hardware.” Under ITAR, that distinction is irrelevant. Code may be export-controlled to the same degree as a physical weapons platform.
III. Autonomous Systems and USML Exposure
Autonomous drones, loitering munitions, ISR systems, and unmanned ground vehicles commonly fall within USML Categories IV, VIII, XII, or related categories depending on capability.
If AI enables:
- Target identification
- Weapons guidance
- Autonomous strike authorization logic
- Electronic-warfare countermeasure optimization
the AI layer is unlikely to be considered commercially separable from the defense article.
DDTC evaluations frequently turn on whether the AI functionality is:
- Uniquely military in purpose
- Optimized for battlefield deployment
- Architecturally embedded at the systems level
The deeper the integration into weapons functionality, the stronger the ITAR nexus.
IV. Targeting Algorithms and Defense-Service Exposure
AI-driven targeting engines present heightened compliance risk.
Such systems may:
- Fuse multi-sensor intelligence
- Prioritize and rank potential targets
- Recommend engagement options
- Optimize strike parameters in real time
If the algorithm materially contributes to weapons deployment capability, it may qualify as ITAR-controlled technical data.
Additionally, furnishing assistance to foreign persons in designing, optimizing, troubleshooting, or integrating such targeting systems may constitute a defense service under ITAR even in the absence of a formal file transfer.
Virtual meetings, whiteboard sessions, and advisory guidance may carry export implications.
V. Cloud Computing, Git Repositories, and Deemed Exports
Modern AI development environments introduce structural compliance vulnerabilities, including:
- Distributed cloud-based compute
- Globally dispersed engineering teams
- Foreign-national software developers
- Git-based version-control access
- Cross-border DevOps pipelines
Deemed Export Risk
ITAR treats disclosure of controlled technical data to a foreign person within the United States as a “deemed export.”
This may include:
- Repository access granted to foreign-national engineers
- Debugging sessions involving controlled code
- Zoom-based system design discussions
Lawful immigration status does not eliminate deemed export exposure. Access controls, not employment classification, determine regulatory outcomes.
VI. AI Training Data: A High-Risk Blind Spot
Training datasets derived from controlled defense systems present a growing compliance exposure.
If a dataset:
- Reflects performance specifications of U.S. Munitions List systems;
- Encodes operational thresholds or targeting parameters;
- Incorporates simulation outputs based on controlled mission scenarios;
it may constitute technical data subject to ITAR.
Classification is driven by informational content—not file type.
VII. ITAR vs. EAR Jurisdictional Analysis
Not all military-adjacent AI falls under ITAR.
Export jurisdiction depends on whether technology is:
- Enumerated on the U.S. Munitions List (ITAR), or
- Controlled under the Export Administration Regulations (EAR), administered by the Bureau of Industry and Security (BIS).
Dual-use AI systems, such as predictive maintenance engines or satellite-image analytics tools, may fall under EAR rather than ITAR.
However, when AI is specially designed or modified for combat systems or integrated into weapons platforms, ITAR jurisdiction becomes more likely.
Commodity Jurisdiction (CJ) requests remain essential where ambiguity exists.
VIII. Enforcement Convergence and Parallel Risk
ITAR enforcement increasingly intersects with:
- Criminal export investigations
- Actions coordinated with the U.S. Department of Justice
- Sanctions-based scrutiny administered by the Office of Foreign Assets Control
- National-security procurement reviews
Regulatory exposure frequently involves:
- Unauthorized defense services
- Technical-data exports without license
- Misclassification
- Inadequate technology control plans
- Governance failures
For venture-backed defense startups, even informal inquiry may materially affect funding, M&A transactions, and government-contract eligibility.
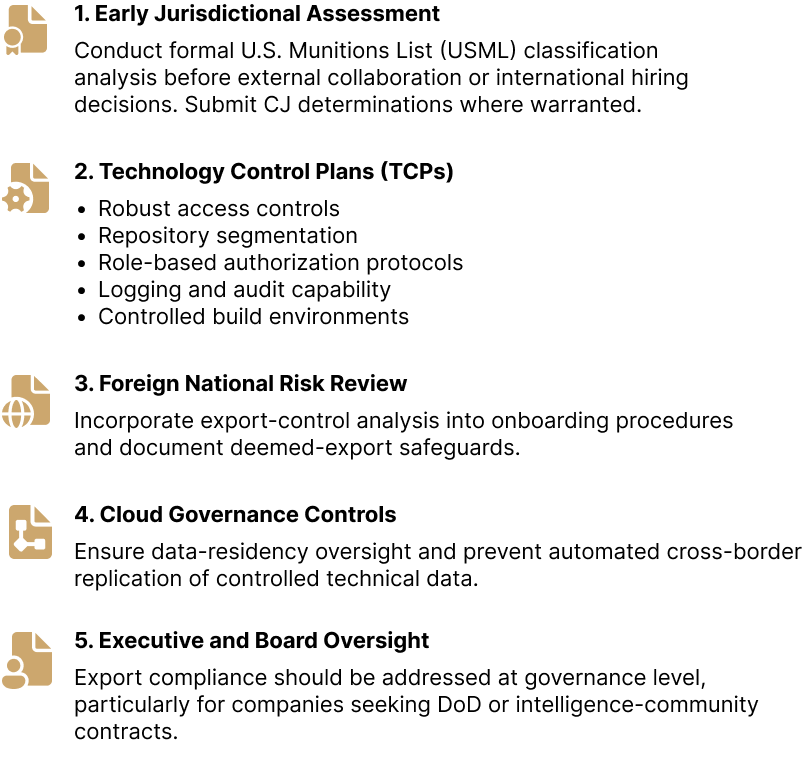
IX. Recommended Compliance Architecture for AI Defense Companies
We recommend structured, proactive compliance measures, including:
Frequently Asked Questions (FAQ)
Can AI source code be controlled under ITAR?
Yes. If it is specially designed or modified for a USML defense article, it may constitute controlled technical data.
Are AI model weights export-controlled?
They may be, if they reflect controlled system characteristics or operational capabilities.
Can granting Git repository access trigger an export?
Yes. Providing foreign persons access to controlled code may constitute a deemed export.
What constitutes a “defense service” in AI development?
Providing training, consulting, optimization, or integration assistance involving controlled defense articles may qualify, even absent data transfer.
Does a Department of Defense contract eliminate ITAR risk?
No. Government contracting status does not substitute for export authorization or compliance obligations.
Is open-source AI automatically exempt?
No. The public-domain exception is narrow and fact-specific. Improper disclosure may itself constitute a violation.
Conclusion
AI-enabled defense technologies fundamentally reshape export-control exposure.
Under ITAR:
- Code can be technical data.
- Consulting can be a defense service.
- Remote collaboration can trigger deemed exports.
- Cloud architecture can create licensing obligations.
Organizations operating at the intersection of artificial intelligence and national security must integrate export-control analysis at the earliest stages of product development.
For companies developing autonomous systems, targeting algorithms, or other military AI applications, export compliance is no longer peripheral, it is structural.

 English
English  Español
Español  Русский
Русский  Turkish
Turkish  Persian (فارسی)
Persian (فارسی)  Arabic (العربية)
Arabic (العربية)  简体中文 (中国)
简体中文 (中国)